What is Phishing?
Phishing attacks are intended to collect your personal data, financial information or install viruses/trojans on your machine. They can be delivered by many methods
- Email: A message containing a link to a malicious website or a faked login form designed to capture your username and password. Typically this mail will offer you something that seems too good to be true (free tokens) or claim you need to visit a link for some urgent reason (to Validate your account or similar)
- Skype & other messengers: People claiming to be Cam4 staff asking you to do something (private shows, an audition, a problem with your account, etc) or again links that may be malicious or images that may be infected.
- Inbox messages: Faked messages saying you received a tip or gift, links requiring login – you may also see these appear in chat
What can you do about it?
- Don’t reveal personal or financial information in an email, and do not respond to email solicitations for this information. This includes following links sent in email.
- Before sending or entering sensitive information online, check the security of the website.
- Pay attention to the website’s URL. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com versus .net). If you look at the site URL in the browser address bar you will see the following
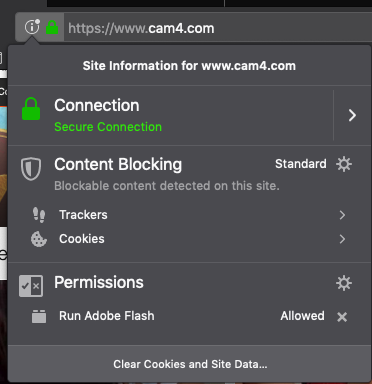
The presence of the padlock to the left of the URL shows that we have the security certificate for the domain and the link is valid. A faked page will not have this. See the example below
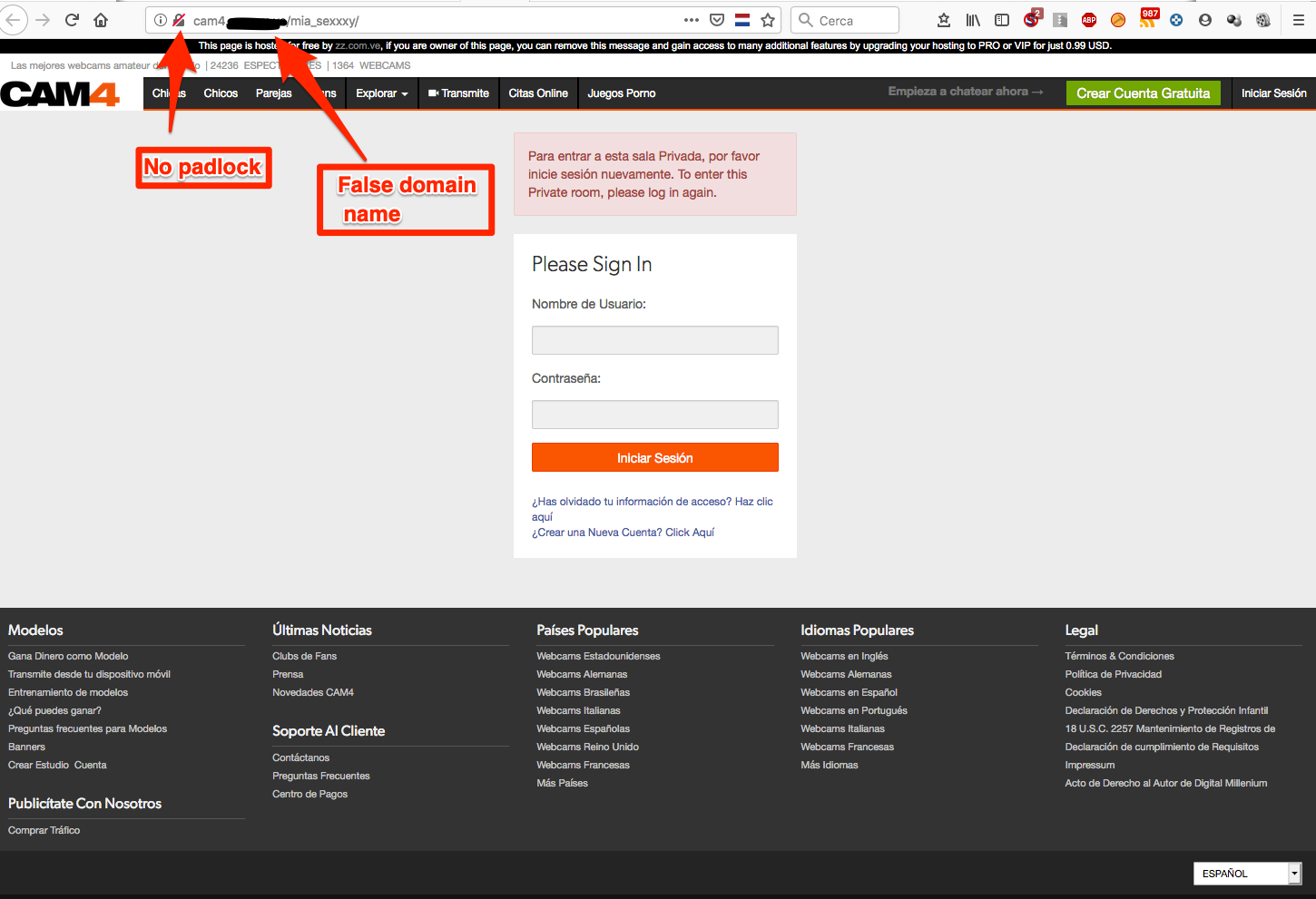
- The padlock shows with a red line through it, showing this is not a secure site
- Note the domain name does include cam4 but is not cam4.com.
Please pay attention to links like this provided through any method, particularly those asking you to login or provide personal information
Protect yourself
- When in doubt, throw it out: Links in email, tweets, posts, Skype etc are often how information is compromised. If it looks suspicious, even if you think you know the source, it’s best to delete or – if appropriate – mark it as junk.
- Think before you act: Be wary of communications that ask you to act immediately, offers something that sounds too good to be true or asks for personal information. If you want to check if the request is valid, please contact us directly at support@cam4.com, do not use the link you received.
- Use a strong password: Make sure you do not use the same password for everything. Some tips on using a good password can be found here
- Lockdown your account: In addition to a good password, make sure to add your security questions for additional protection. You can also add 2-factor authentication by using our SMS verification system
